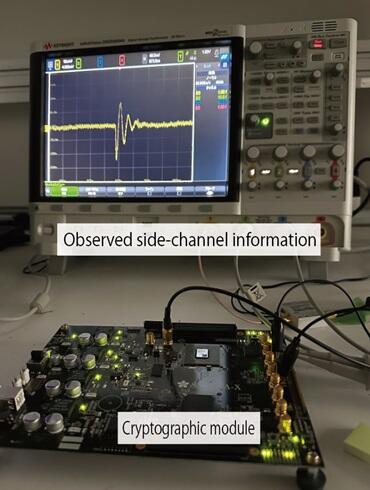
Today, personal and financial information is exchanged over the internet. As a countermeasure against cyberattacks, "cryptographic modules" that encrypt information have been embedded within information and communication devices. However, some cyberattacks exploit the physical weaknesses of these modules - more specifically, "side-channel attacks" - capitalize on secondary physical information, such as power consumption and emitted electromagnetic waves that are generated during module operation. These attacks are non-destructive, leave no traces, and can be carried out without contact. Research and development on cryptographic modules capable of withstanding such attacks is being undertaken worldwide. Existing methods are very costly due to their reduced speed and increased power consumption.
In response to these issues, a research group led by Professor Naofumi Homma of the Research Institute of Electrical Communication at Tohoku University, has developed a new method for regenerating and switching cryptographic keys, known as "rekeying (key replacing)." This method can be implemented in cryptographic modules at less than one-tenth the cost of conventional methods because it does not require any special circuit technology. Even if the module contains components vulnerable to attacks, the module can be robustly protected for a long period by appropriately replacing the encryption key. Demonstrations have shown that even under the most powerful side-channel attacks, the period of endurance against attacks can be extended exponentially.
The newly developed technology enables the implementation of cryptographic modules with high general usability and low cost while physically and mathematically guaranteeing long-term security. The research group plans to apply this technology to small cost-constrained devices and verify its effectiveness, with the aim of improving the security and performance of information and communication devices and systems that use cryptography in the future.